ASSUMPTION
This gives the example of business scenario illustrating the business needs, and the IT service offering in terms of technical design, resource alignment and project management.
It helps customer quickly understand how BROCENT team is delivering the IT managed service.
Manufacturing
Industry
New IT Setup
Statement of Work
Shanghai, China
Applicable Cities
English, Mandarin
Language
50+ Users
User Size
Token Service
Service Type
THE TECHNOLOGIES INVOLVED
In this scenario, the complete IT setup covers EUC computer, printer, network, server, cloud service and security hardening. This section illustrates the key technical elements we have taken care in the IT infrastructure design.
Windows 10 Pro

Switch & Router

Firewall

Hypervisor

Computer &Server

Antivirus
Cloud Wireless

Microsoft 365

Data Backup
End Point Security

Cloud Data Backup

Telephone System

CONCERNS & EXPECTATION
The customer plans to establish the new manufacturing plant in Shanghai, China, and at the same time, it is planned to close the existing plant in Beijing. Customer CIO concerns much about technical implementation &transition plan if it could meet the "1 Month" target timeframe, while it would not compromise any technical standards and expectation on quality and communication &time zone gap.
BUSINESS REQUIREMENT AND ARCHITECTURE DESIGN
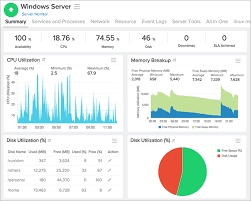
SERVERS & STORAGE
- Needs a robust physical server, that supports VMWARE virtualization to host multiple hosts and roles of Domain Controller, DNS, DHCP, SQL Server, Accounting System, File server etc.
- A cost effective NAS storage as a backup media to contain the business backup data with capacity of retaining data up to one year
- Use preferred backup solution VEEAM to execute the backup task to cover the application availability and data recoverability.
 |  |  |
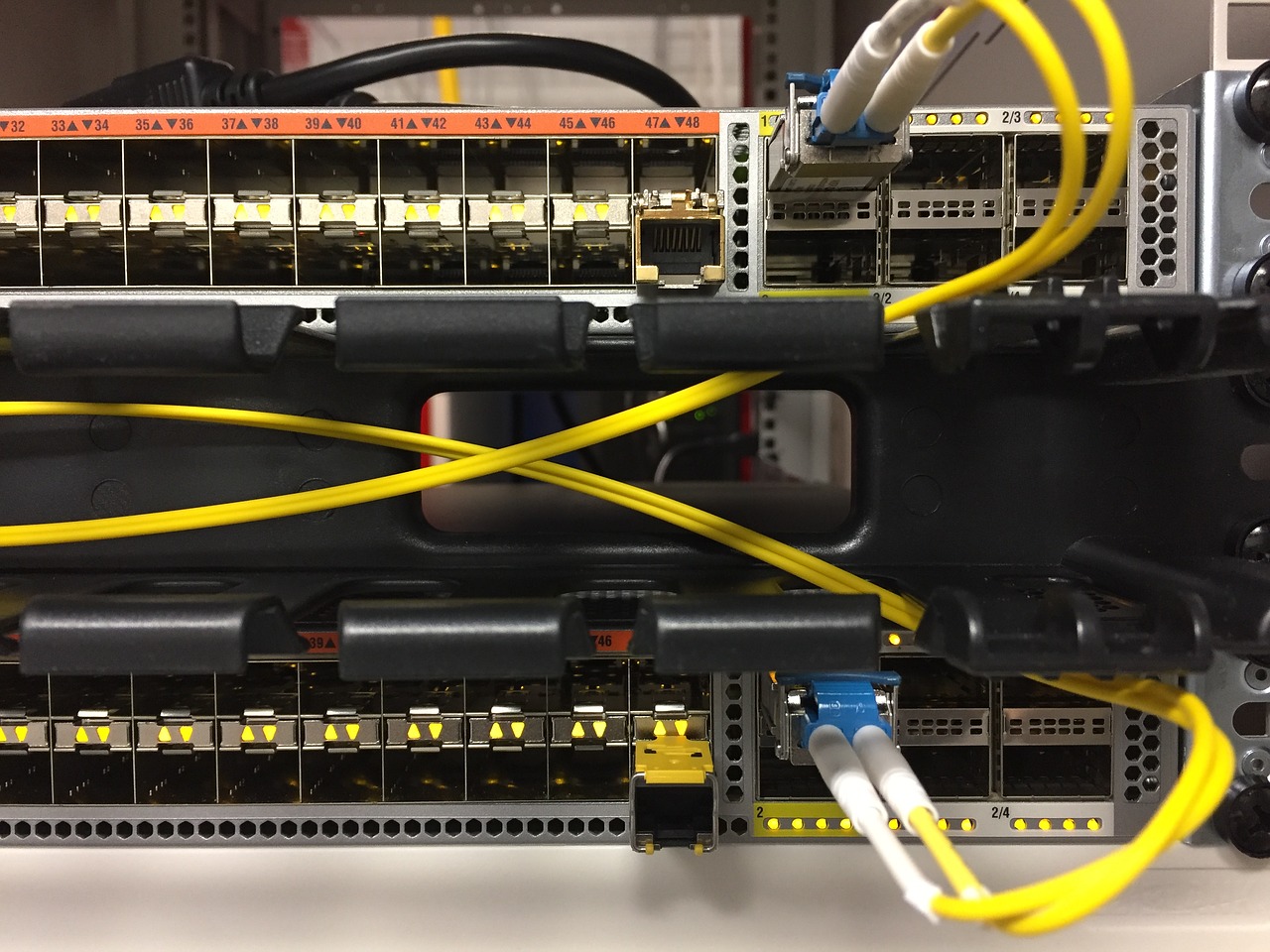
NETWORK
- 2 台の専用 CISCO ルータは、異なる認可ユーザからのネットワーク アクセスの分離を実現するために、エッジ インターネットと MPLS 回線接続をサポートするように設計されています。CISCO VPN は、旅行者や自宅でのモバイル作業をセットアップして許可する必要があります。
- 冗長性を備えた物理的に分離された LAN ネットワークは、特定の VLAN と QOS を使用してデータおよび音声ネットワークを管理し、転送速度とスケーラビリティを保証するように設計されています。
- 指定ファイアウォールは、レッドゾーンからネットワークアクセス制御を管理し、Webフィルタリング機能を使用して、ウイルス対策、スパイウェア、不審なインターネットデータの観点からイントラネットのセキュリティを保護するように設定されています


CLOUD SOLUTIONS
Client has strong demand of business contingency plan (BCP), hence requires a flexible solution in the cloud to make sure best system availability. With this needs, BROCENT proposes to setup the cloud backup, accounting system in the cloud, Microsoft 365 email and Sharepoint in the cloud, antivirus in the cloud and so on.
Besides, a office 365 new tenant needs to subscribed respectively in China mainland and Hong Kong to support two business units with unique domain name. Prerequisite requirement is to make data migration from Lotus Domino on-premise servers to Office 365 cloud service with all business email data, calendar, Directory and archived data. As a higher priority task, BROCENT uses authorized migration tools and migrated 4.2T data into Office 365, and all users are happy to use Microsoft outlook after the post-implementation training.

COMPUTER & PRINTER
Group standard computer model and specification is designed to meet the business requirement from production department, R&D department and back office needs with standard Windows 10 Enterprise preloaded OS and standard EUC operating environment i.e., patch management, password policy, power user account, standard list of software.
All computers are part of Active Directory for central management in terms of group policy, user account and password management, and the single sign-on settings integrated with Office 365.
IT ROOM &ENVIRONMENT MANAGEMENT
顧客のITインフラストラクチャ要件は、工場内の50人以上のユーザーとコンピュータ化されたシステムをサポートするサーバールームと施設を設計することです。
物理的なセキュリティの面では、それはまた、CCTV、湿度と温度センサー、A / Cモニターとドアアクセス制御システムで設計されています。
GOODS SUPPLY & COMPLIANCE
Bill of Materials (BOM) are agreed to make sure every single elements in the design is thoroughly considered and assessed. With better planning comes more accurate knowledge on how much time a task will take. This allows Solution Team and Customer to cost up jobs and orders more effectively. In Asia, usually the delivery of goods ordered directly from manufacturer costs 4 weeks to 8 weeks, knowing that it gives roughly precise estimation on goods lead time, and gives better assumption when to prepare the project plan. For the sake of IT compliance, BROCENT never works on refurbished, unofficial and unlicensed IT products.